http://www.v3.co.uk/v3/news/2245583/twitter-users-warned-job-scams
It seems like common sense that most people realize “get rich quick” schemes aren’t worth pursuing. However, just like in the height of the Tech Boom of the late ’90’s it seems that people are rationalizing that “things are different” when it comes to Twitter.
Certainly there are some new ways to market products using Twitter, and the fact that Twitter updates can only be 140 characters begs the question “How hard can it be?”
So, it’s not much of a surprise that “get rich quick” scams will find ways to trick people into either giving up personal information, or paying up front for tips on how to make a fortune while lying in bed in your pajamas. But people want to believe it’s still possible to have good fortune, if only they can get the timing right.
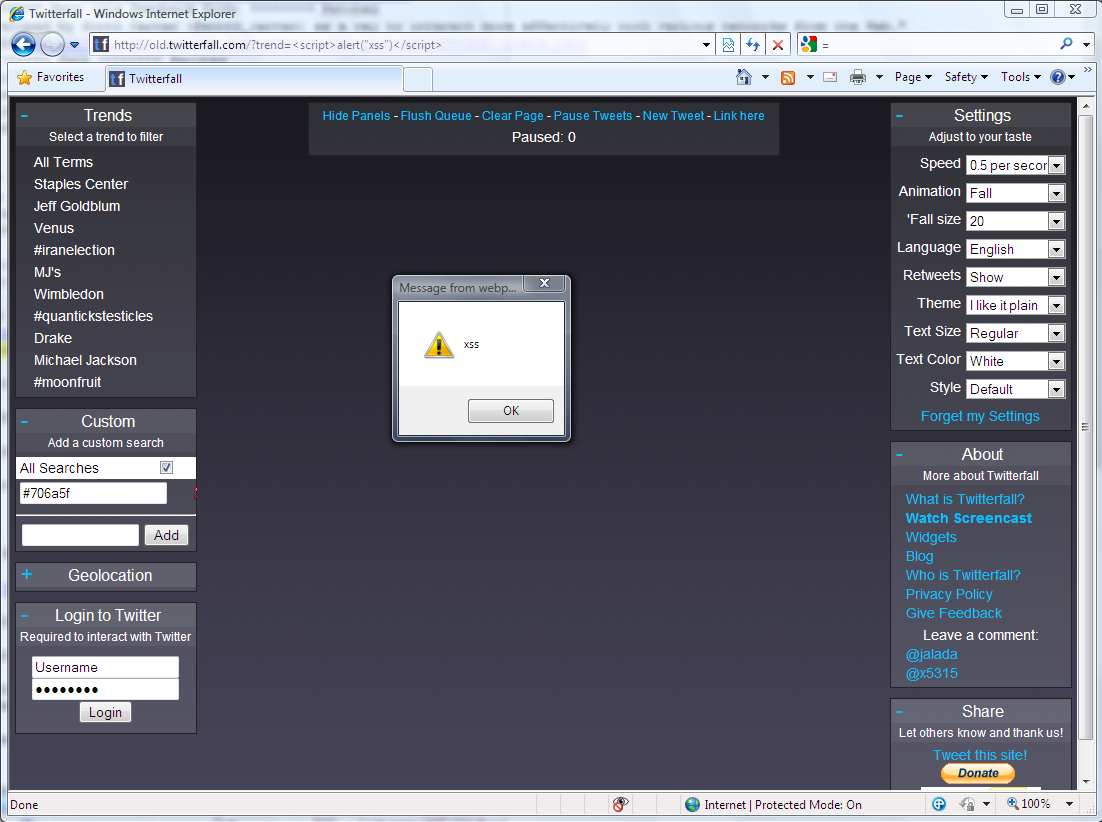
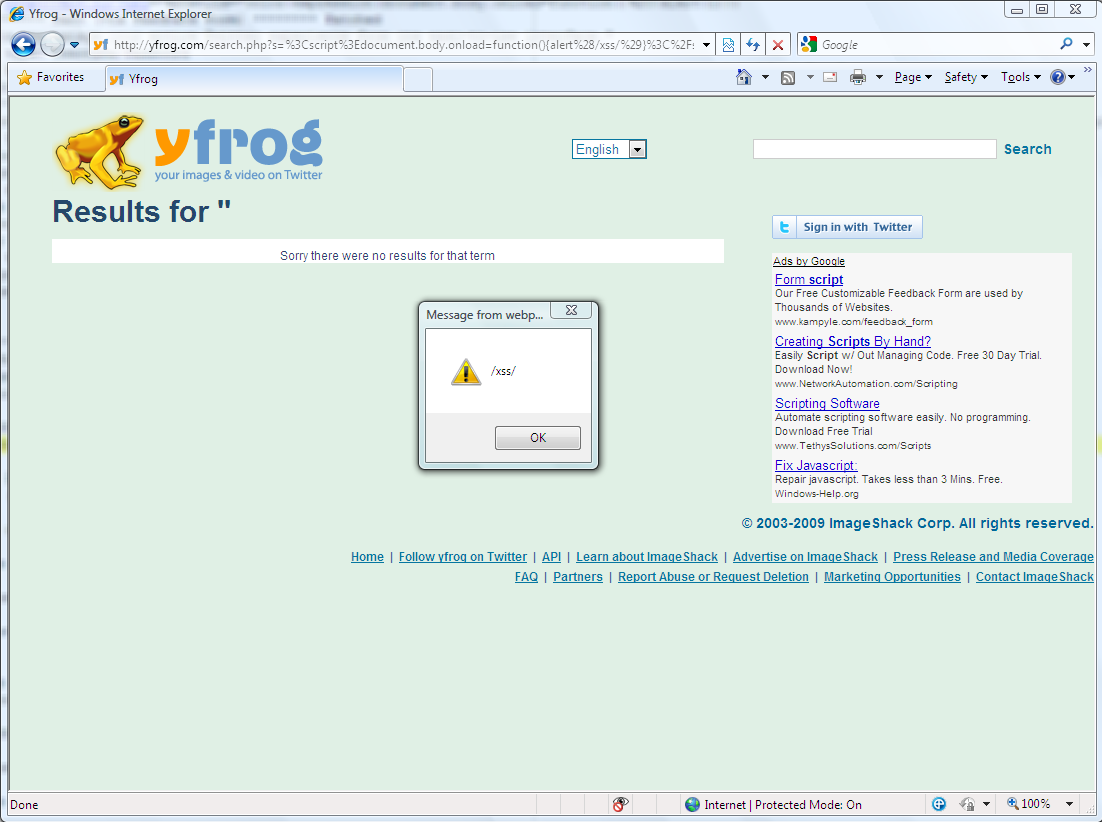
Indeed, new trends are emerging so quickly, it might be tempting to feel that you can “get in on the ground floor” of a new business model. But Twitter is a double-edged sword in that it allows attackers to create compelling headlines and hide their malicous intent and websites in shortened links that many people will click on without considering the risks.
Twitter can be used as a way to quickly reach hundred or thousands of followers. But as with any scheme that sounds too good to be true… Twitter-based opportunities deserve just as much scepticism as any other.
I am now offering monthly briefings, tailored to organizations that want to build and sustain security awareness for staff. Just because your security team is too busy to do its own training and awareness doesn’t mean you can’t have an economical way to address human security risks. Please call or email me at the coordinates below…
Scott Wright
The Streetwise Security Coach
Join the Streetwise Security Zone at:
http://www.streetwise-security-zone.com/join.html
Phone: 1-613-693-0997
Email: scott@streetwise-security-zone.com
Twitter ID: http://www.twitter.com/streetsec
To receive weekly security tips and other notices about helpful content available on this site, please make sure you are on my list by clicking HERE, and entering your name and email address.