What is bit.ly
“bit.ly allows users to shorten, share, and track links (URLs). Reducing the URL length makes sharing easier. bit.ly can be accessed through our website, bookmarklets and a robust and open API. bit.ly is also integrated into several popular third-party tools such as Tweetdeck.” (bit.ly )
Twitter affect
bit.ly can be used to send tweets with the shortened URLs through a form on their website, or a simple GET request.
bit.ly is using the OAuth authentication tokens in order to send tweets via the Twitter API.
Popularity rate
Second most popular URL shortening service in the wild – 4.5 twits





Vulnerabilities
1) Reflected Cross-Site Scripting in the “url” query parameter.
Status: Patched.
Details: This vulnerability was first reported by Mario Heiderich on May 18th 2009, on twitter.
A week later, I found that this vulnerability got fixed. Unfortunately, after playing with it a bit, I figured that it was only partially fixed. Instead of encoding the HTML entities, bit.ly developers have decided to strip the <> characters. E.g. this proof-of-concept would have popup an alert on IE7:
htttp://bit.ly/?url=”%20style=”color:expression(document.body.onload=function()%20{alert(1)})
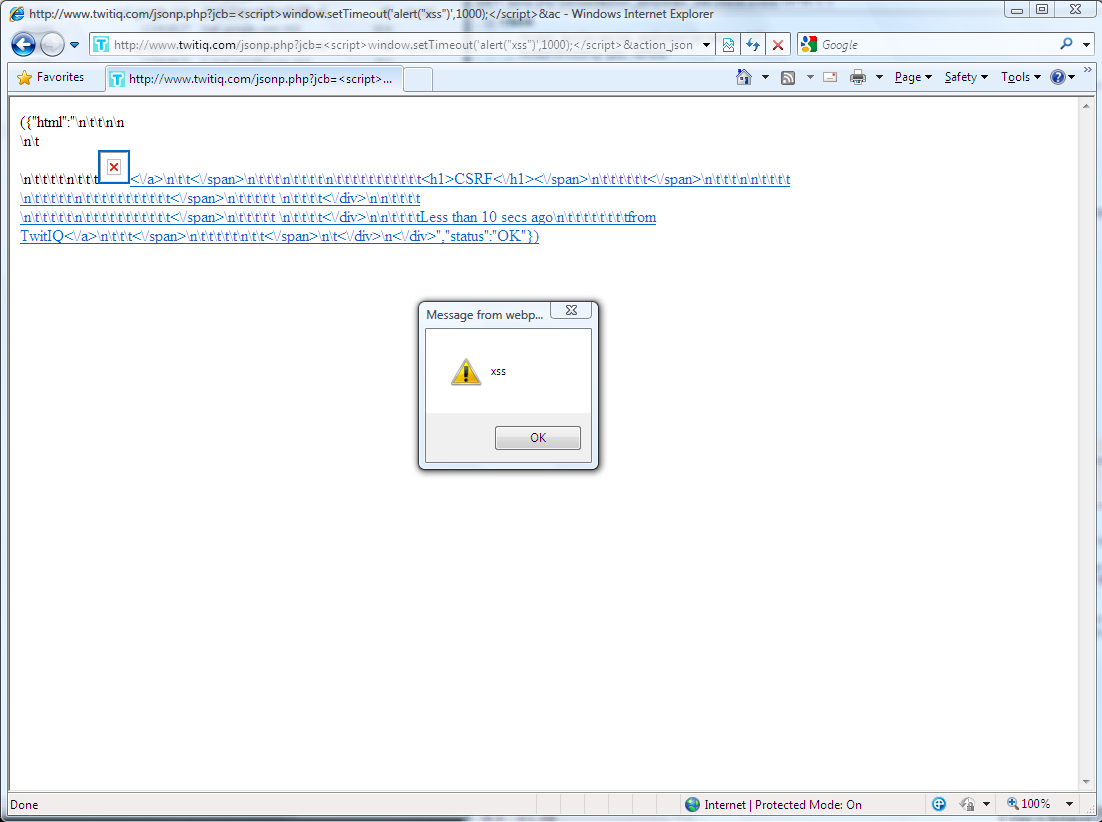
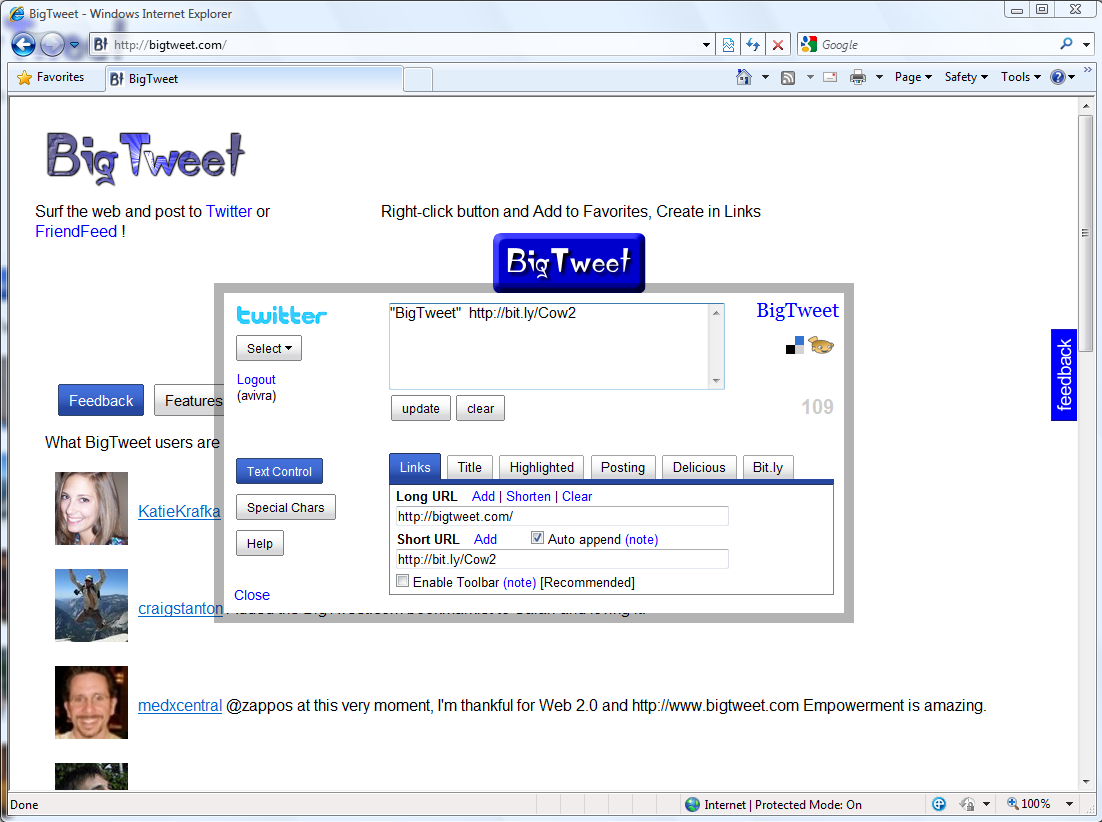
The following is the screenshot of the PoC:

Several days ago, after a long discussion with Mario, bit.ly has finally fully fixed this vulnerability.
2) Reflected Cross-Site Scripting in the keywords parameter.
Status: Patched.
Details: This vulnerability was reported by Mike Bailey on June 24th 2009. See Mike’s advisory for more details: http://skeptikal.org/2009/06/parsing-quirk-causes-bitly-xss.html
This vulnerability was fixed by bit.ly yesterday.
3) Reflected POST Cross-Site Scripting in the username field of the login page
Status: Patched
Details: This vulnerability was reported by Mario Heiderich. See Mario’s advisory for more details: http://heideri.ch/bit.ly.txt
This vulnerability was fixed by bit.ly yesterday.
4) Persistent Cross-Site Scripting in the content-type field of the URL info page
Status: *Unpatched* Patched.
Details: This vulnerability was submitted by Mike Bailey on June 25th 2009.
Whenever a URL of a website gets shortened by bit.ly service, an information page is created for the URL, with statistics and metadata about the website.
One of the metadata information being stored by bit.ly is the content-type response header of the shortened URL page. This information of-course can be easily changed.
bit.ly fails to encode HTML entities while displaying the content-type information, and therefore allows injection of scripts to the page.
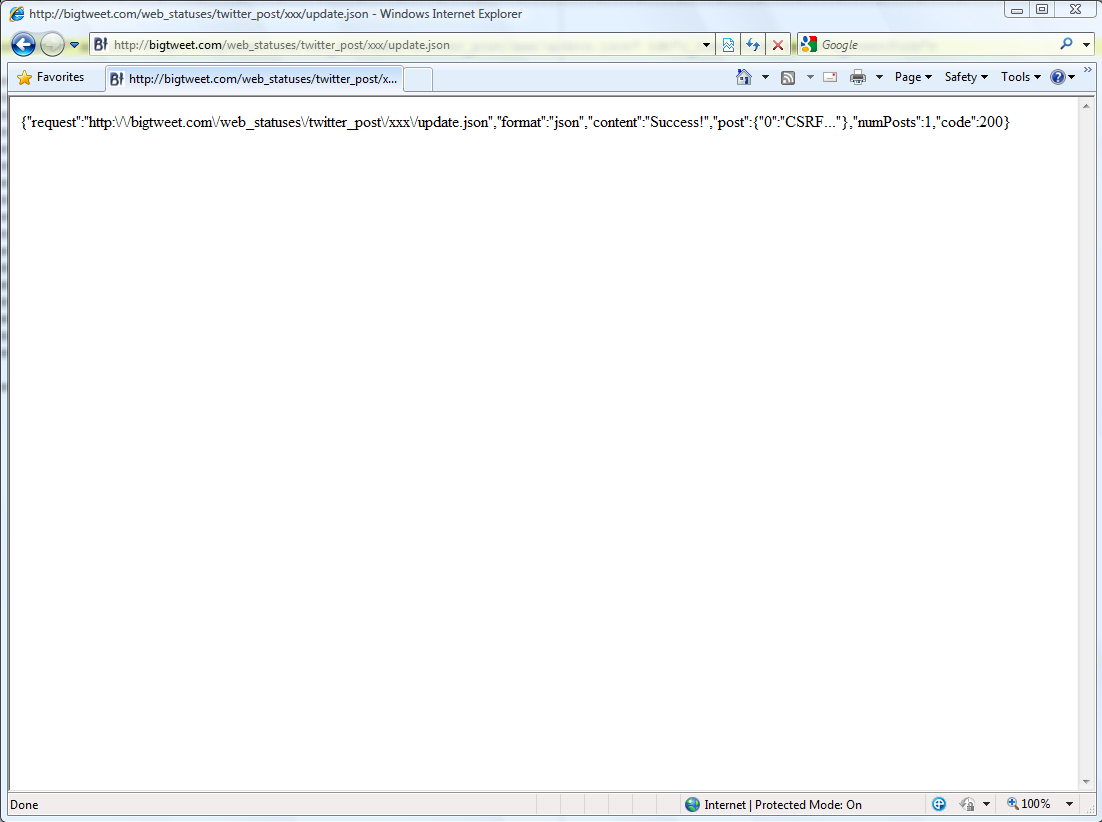
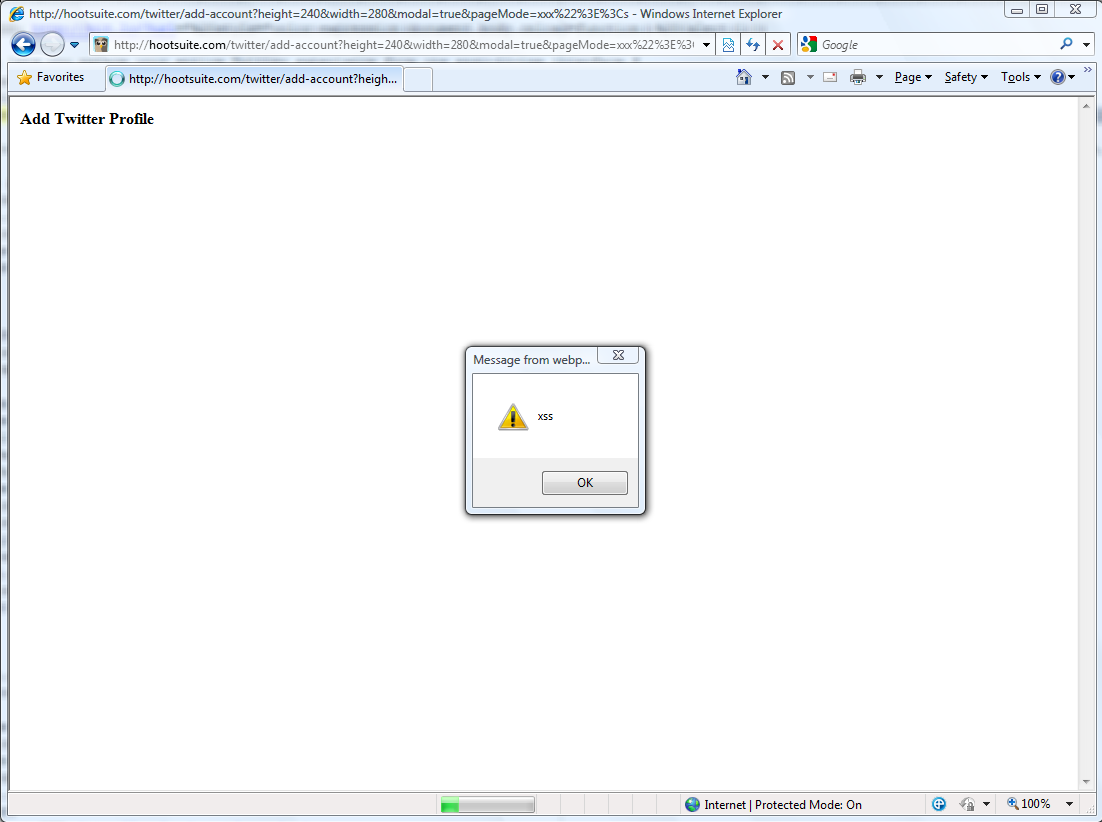
Live proof-of-concept can be found here:
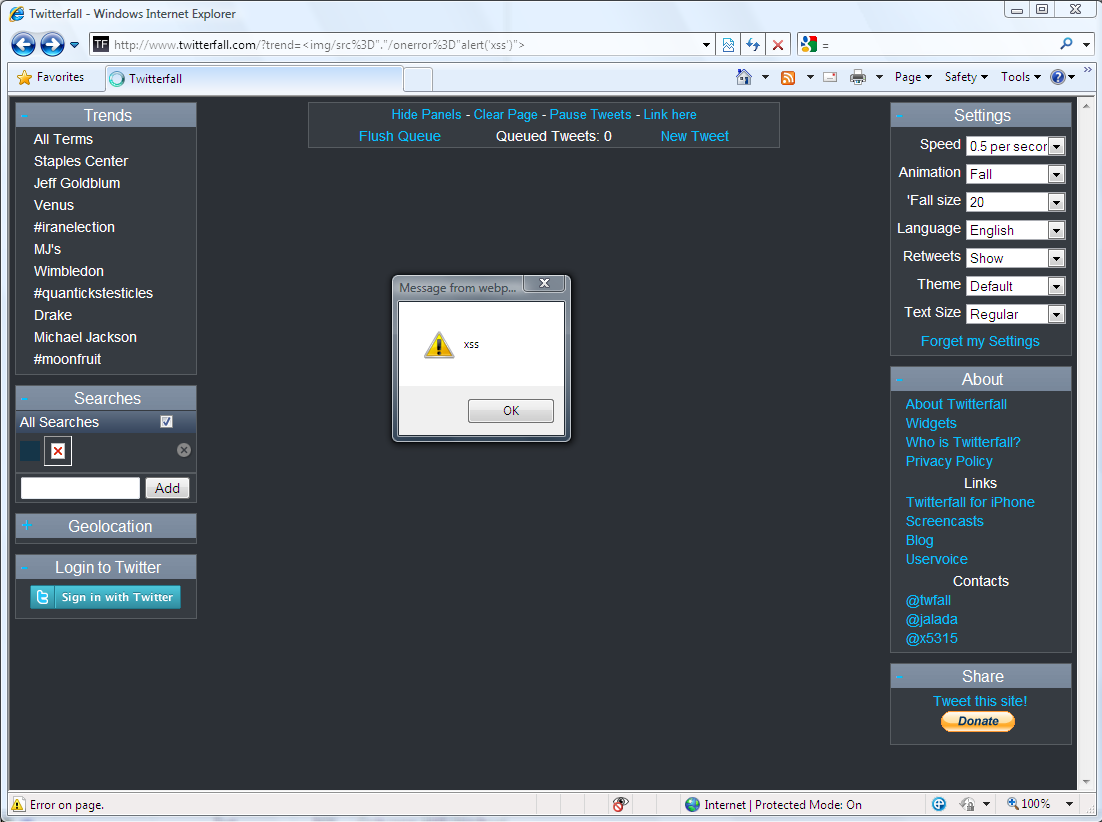
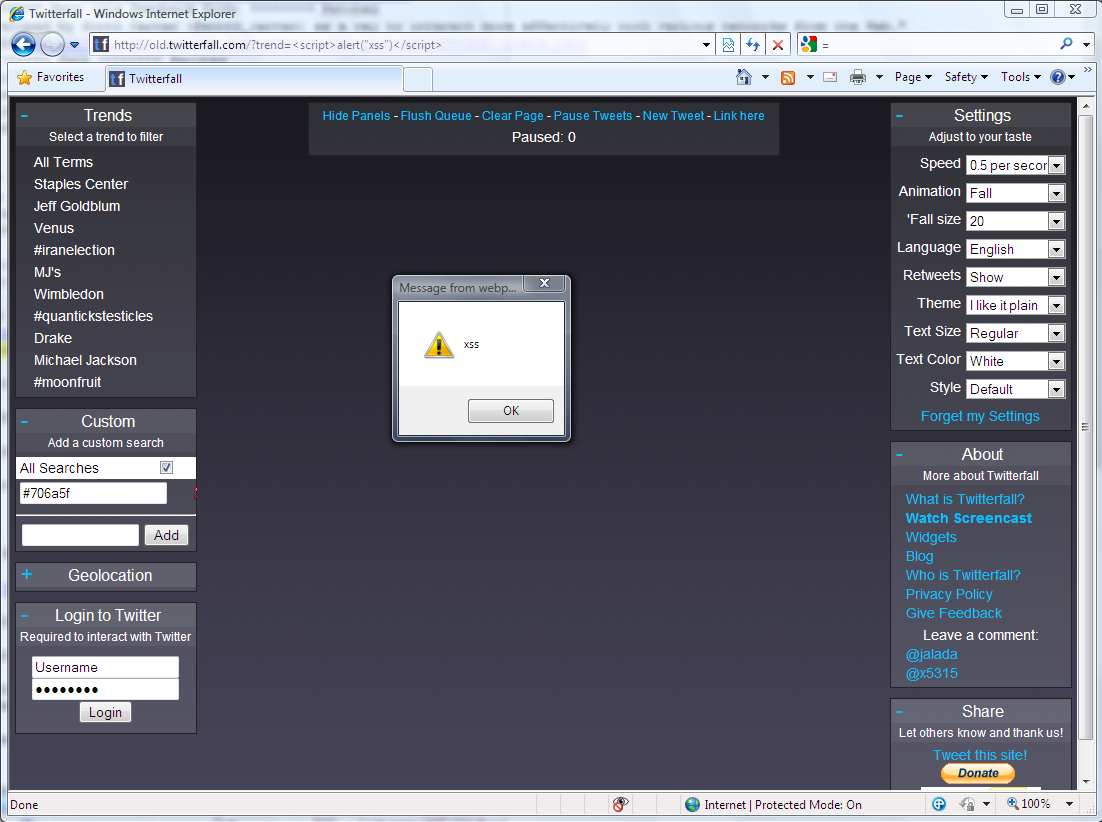
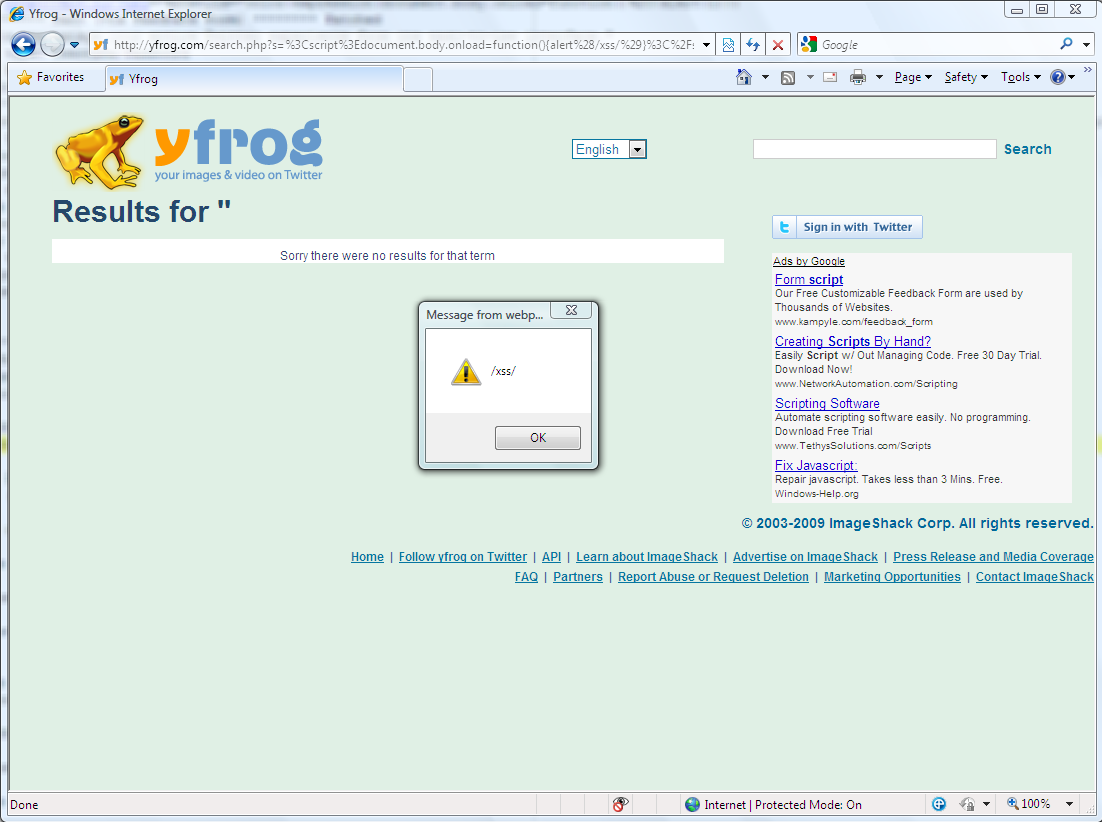
Screenshot of the PoC (just in case the live demo will be removed):

Vendor response rate
It took bit.ly a month and a half to fix simple XSS vulnerabilities. Very poor – 0.5 twits.

In conclusion
bit.ly has a large user base (who doesn’t click bit.ly links?). However, with such a poor response rate to security vulnerabilities, and with such a poorly coded website, in terms of security, we can only hope for the best. Please be careful clicking those shortened URLs…
[Update – 3 hours into Month of Twitter Bugs] bit.ly have finally fixed the last vulnerability.